Microsoft quickly addressed CVE-2026-20841 in their February 2026 Patch Tuesday updates. The patched version finally sanitizes the URI handlers and neutralizes special command elements before they ever reach the shell.
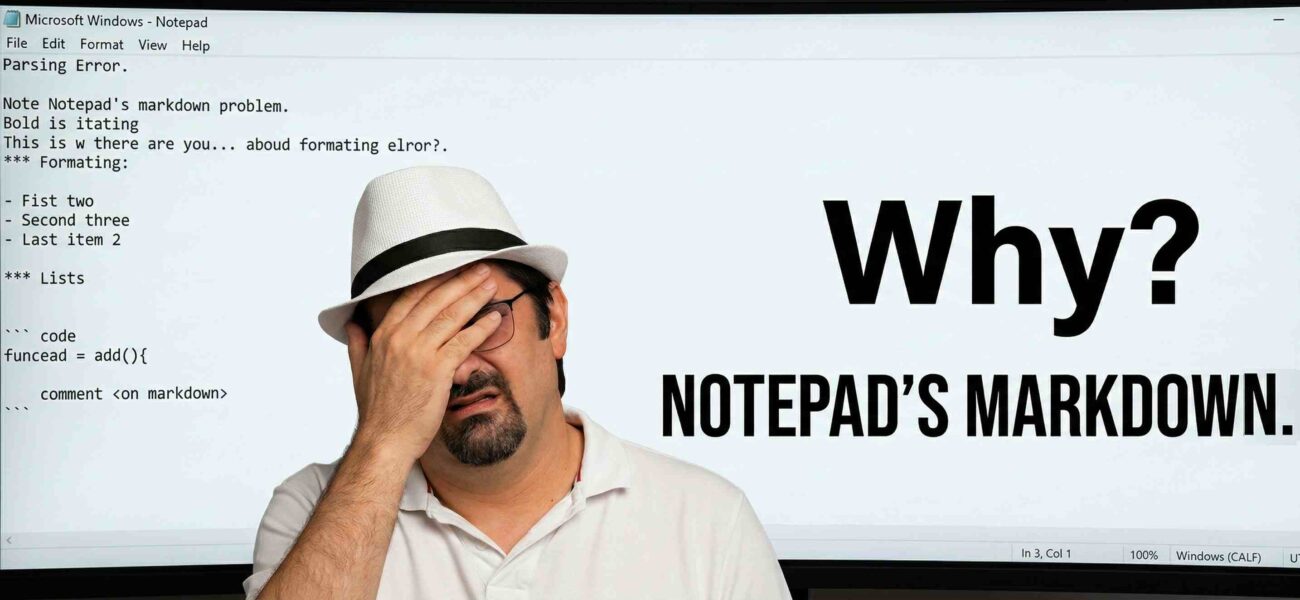
How a “Dumb” App Got Too Smart
Historically, Notepad was famously secure simply because it didn’t do anything complex. It rendered raw text. Zero attack surface. However, modern versions of Windows 11 introduced a seemingly innocent feature: Markdown support.
When you open a .md file in the updated Notepad, it no longer just displays raw text. It actively parses the document. This means if you type standard Markdown link syntax: [display text](URL)
Notepad converts it into a clickable hyperlink!!
The Exploit: A Direct Pipe to the Shell
The vulnerability lies in how Notepad handles that link when a user actually clicks it. The development team implemented the feature in the most literal, trusting way possible.
Here is the step-by-step breakdown of the failure:
- Parsing: Notepad reads the Markdown link structure.
- Extraction: It extracts the raw URL string provided by the author of the file.
- Execution (The Fatal Flaw): It passes that exact, unvalidated string directly into the Windows API function
ShellExecuteExW.
By passing unsanitized input directly into ShellExecuteExW, Notepad blindly trusts the string. This API function is incredibly powerful; it isn’t just for opening https:// web pages in a browser. It utilizes configured Windows protocol handlers to execute commands.
An attacker doesn’t need to craft a complex memory corruption exploit or buffer overflow. They just need to trick a user into opening a malicious .md file and clicking a link.
The Attack Vectors:
- Local Binaries: Using
file://protocols to launch local executables or trigger scripts already planted on the machine. - App Installers: Using
ms-appinstaller://protocols to force the system to download and install attacker-controlled applications from a remote server. - Arbitrary Parameters: Passing command-line arguments directly to native tools like
cmd.exeor PowerShell.